[Date Prev][Date Next][Thread Prev][Thread Next][Date Index][Thread Index]
[Full-disclosure] [Wooyun] Safari for windows PhishingAlert bypass vuln
- To: full-disclosure@xxxxxxxxxxxxxxxxx
- Subject: [Full-disclosure] [Wooyun] Safari for windows PhishingAlert bypass vuln
- From: "Wooyun.org" <help.en@xxxxxxxxxx>
- Date: Thu, 26 Dec 2013 23:00:28 +0800
*Abstract:*
The PhishingAlert of Safari stops functioning in Windows systems if an
abnormal URL is being used.
*Details:*
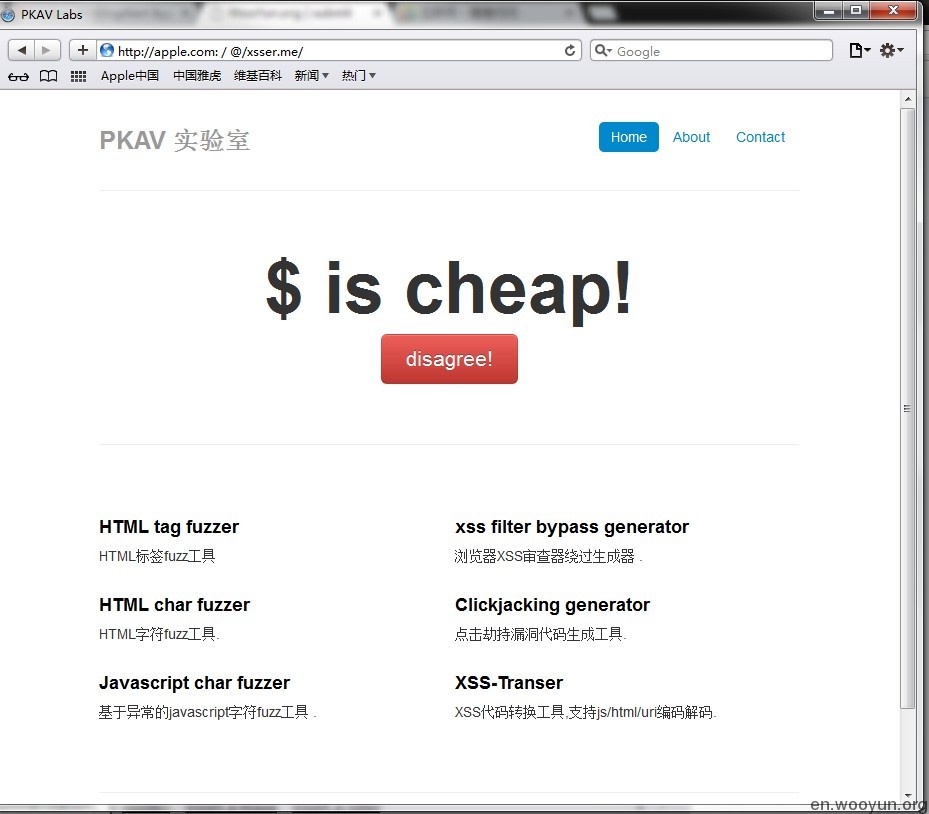
There is a defense mechanism in Safari which recognizes URL deceits such as
http://www.baidu.com@xxxxxxxx. The phishing alert will be activated once
the HTTP URL that we want to access contains userinfo information.
(as the picture below shows)
[image: 内嵌图片 1]
> http://apple.com@xxxxxxxx/
*Proofs of concept:*
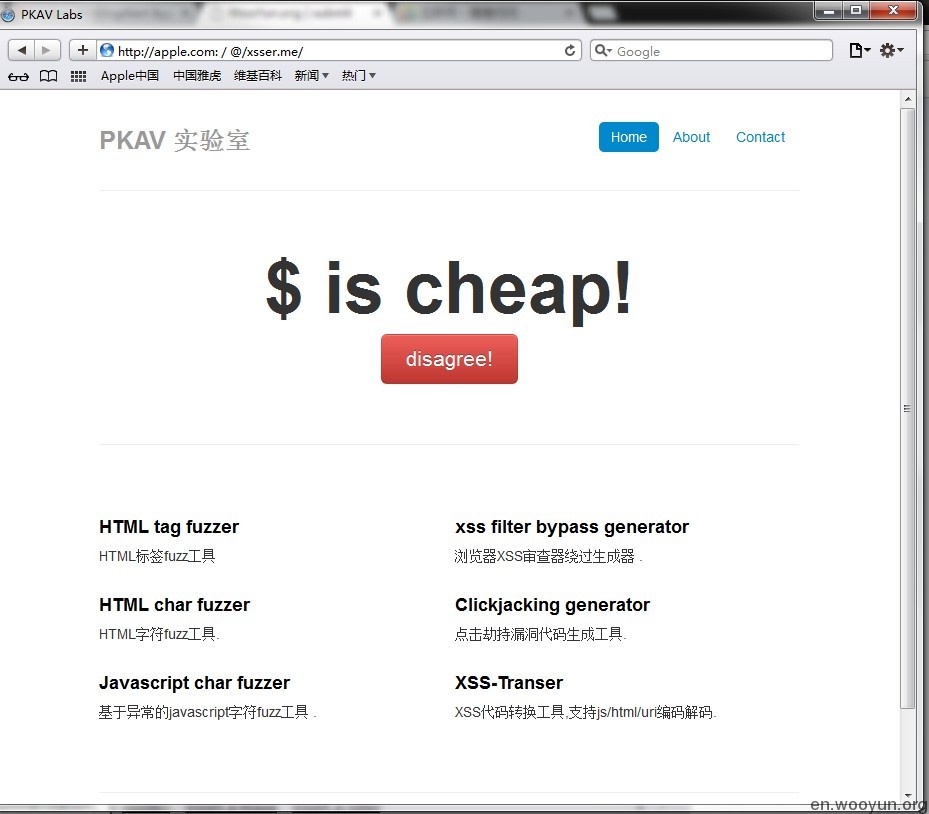
We discovered in our researches that if one or two “/” are being added
before the host name, then the PhishingAlert could be bypassed. (Password
of userinfo must be available)
[image: 内嵌图片 2]
http://apple.com:/@/xsser.me/
*From:*http://en.wooyun.org/bugs/wooyun-2013-014
--
WooYun, an Open and Free Vulnerability Reporting Platform
For more information, please visit *http://en.wooyun.org/about.php
<http://en.wooyun.org/about.php?>*

_______________________________________________
Full-Disclosure - We believe in it.
Charter: http://lists.grok.org.uk/full-disclosure-charter.html
Hosted and sponsored by Secunia - http://secunia.com/